HASH on Twitter: "Guess what we've been playing with... and you can, too! https://t.co/sxIOHZCCZL GPT-3 generates a virtual world in HASH… https://t.co/AWAsqfCGCz"
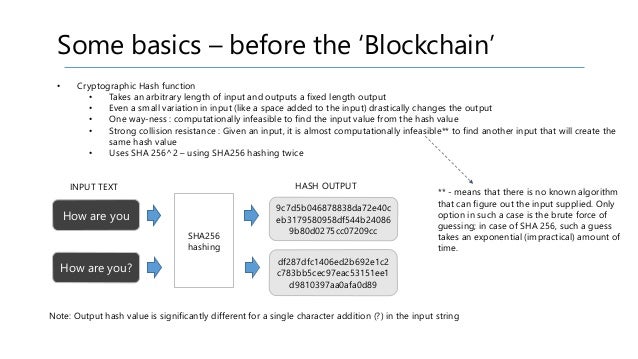
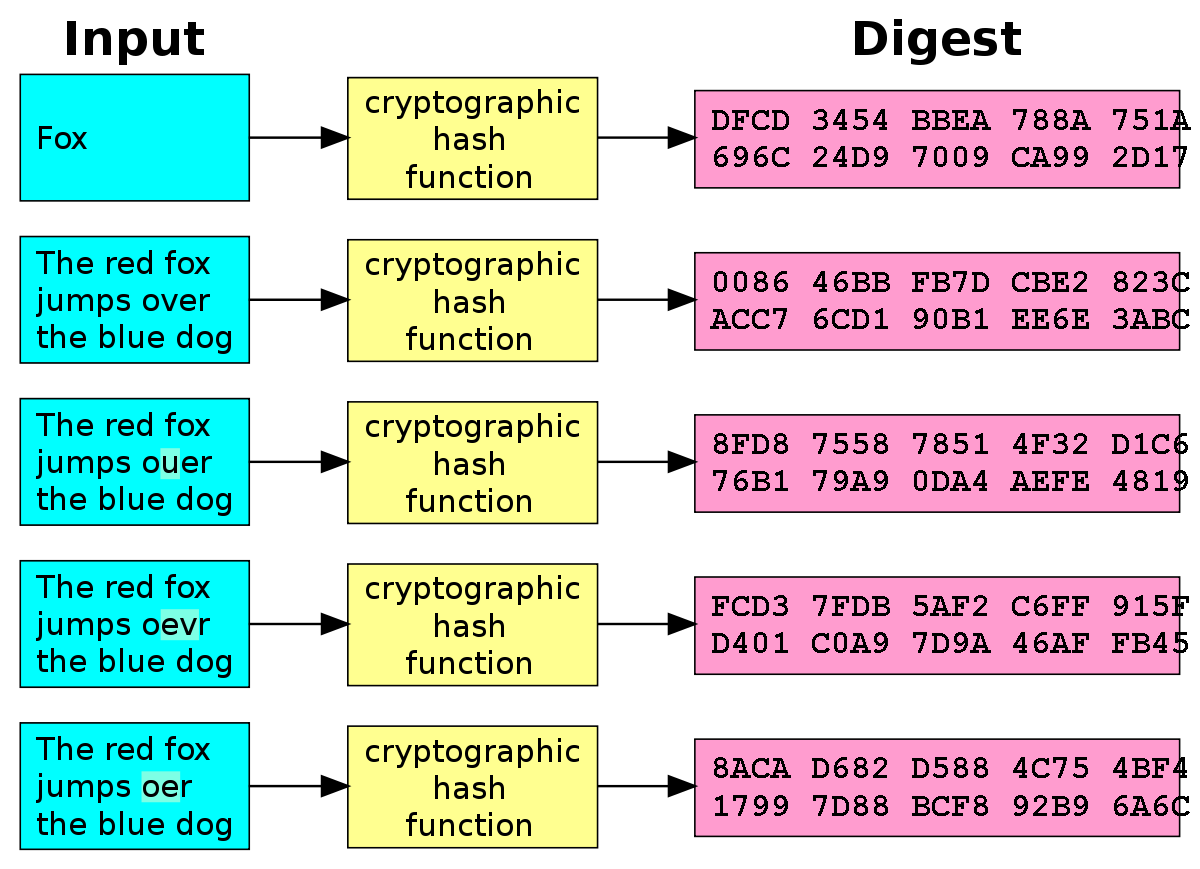
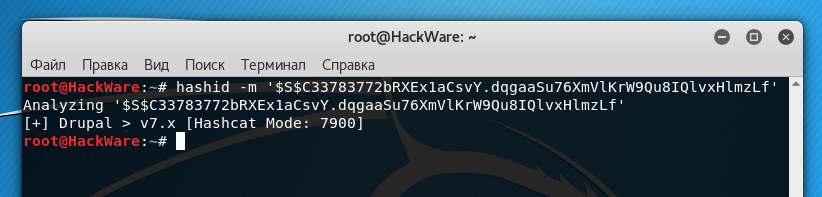
Identifying and Cracking Hashes. During a penetration test or a simple… | by Mr. Robot | InfoSec Adventures | Medium